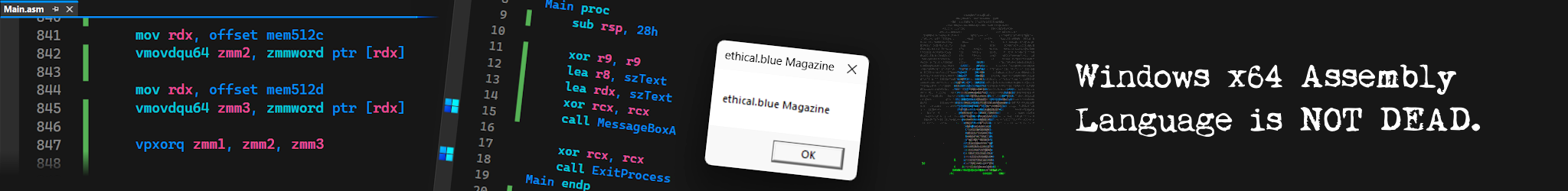
Windows Shortcut Files (.lnk) with Embedded Malware Code
Złośliwy kod w plikach skrótu (.lnk) systemu Windows
Windows Shortcut Files (.lnk) with Embedded Malware Code
Złośliwy kod w plikach skrótu (.lnk) systemu Windows
Computer Viruses //
 ethical.blue Magazine
ethical.blue Magazine

Wirtualna sieć prywatna NordVPN® szyfruje Twoje połączenie internetowe oraz chroni Twój adres IP, co utrudnia podsłuch Twojej aktywności oraz zwiększa bezpieczeństwo przesyłanych danych.

Oprogramowanie F‑Secure® ochroni Twoje urządzenia takie jak komputer czy smartfon przed wirusami komputerowymi oraz złośliwym oprogramowaniem (ang. malware).

„Dobrze, że przenosisz taką wiedzę na polskie ziemie.”
ethical.blue Magazine
to edukacyjne
czasopismo internetowe o wirusach
komputerowych i złośliwym
oprogramowaniu (ang. malware).
Poczta internetowa:
magazine@ethical.blue